Questões de Concurso Público Prefeitura de Niterói - RJ 2018 para Analista de Políticas Públicas e Gestão Governamental - Gestão de Tecnologia
Foram encontradas 80 questões
Pedro é o proprietário do arquivo header.txt em um sistema Linux e gostaria de assegurar que somente ele tivesse permissão de leitura, gravação e execução a este arquivo, enquanto que todos os demais usuários com acesso ao sistema tivessem somente a permissão de leitura.
Assinale a opção que indica o comando que pode ser usado para conseguir esse objetivo.
O RAID é a tecnologia que monta arranjos de discos com a finalidade de aprimorar a segurança e/ou desempenho. Em relação aos níveis de RAID, analise as afirmativas a seguir.
I. RAID 0 divide os dados em pequenos segmentos e os distribui entre os discos disponíveis.
II. RAID 1 usa espelhamento para armazenar os dados em duas ou mais unidades.
III. RAID 10 exige ao menos 3 discos, pois nesse arranjo um disco é dedicado para armazenar a informação de paridade necessária para detecção de erro.
Está correto o que se afirma em
Sobre sistemas de arquivos, analise as afirmativas a seguir.
I. FAT32 utiliza 16 bits para o endereçamento de dados.
II. O tamanho máximo do nome de arquivo no sistema Ext2 é de 1024 bytes.
III. NTFS permite definir os usuários do sistema que podem ter acesso de leitura a determinados arquivos.
Está correto o que se afirma em
A topologia de uma rede de computadores determina como os dispositivos da rede estão interconectados uns nos outros. Em relação às topologias de rede, analise as afirmativas a seguir.
I. Em uma rede em estrela os dados são transmitidos unidirecionalmente de nó em nó até atingir o seu destino.
II. Na rede em barramento é necessário estabelecer um mecanismo de arbitragem para resolver conflitos para o caso de duas ou mais máquinas tentarem fazer uma transmissão simultaneamente.
III. Na topologia em anel os dispositivos da rede são conectados a um switch central responsável por encaminhar os dados especificamente para as estações de destino.
Está correto o que se afirma em
Sobre as técnicas de comutação, analise as afirmativas a seguir.
I. Diferentes pacotes podem seguir caminhos distintos na comutação de pacotes implementada por datagramas.
II. A comutação de circuitos utiliza a transmissão store-and-forward, desde o transmissor até o receptor.
III. Em um circuito virtual os dados são entregues fora de ordem.
Está correto o que se afirma em
As falhas de segurança em sistemas operacionais ou em aplicativos podem permitir que pessoas não autorizadas acessem informações de computadores e instalem vírus ou aplicativos de controle sobre máquinas remotas.
Essas falhas de segurança são denominadas
O correio eletrônico figura entre os principais métodos utilizados para enviar e receber mensagens através da Internet.
Assinale a opção que indica protocolos de comunicação projetados para o gerenciamento de correio eletrônico.
O protocolo HTTP (Hypertext Transfer Protocol) é a base para a comunicação de hipertexto na Internet.
Sobre esse protocolo, analise as afirmativas a seguir.
I. O código de status presente na resposta HTTP é formado por três dígitos, sendo o valor 200 a indicação de que a requisição do cliente foi bem-sucedida.
II. Variáveis ocultas dentro de formulários web e cookies são mecanismos que podem ser utilizados para reter informações ou estado sobre cada usuário entre duas requisições HTTP.
III. O cabeçalho Accept-Encoding na requisição HTTP é utilizado para restringir as codificações de conteúdo que são aceitáveis na resposta do servidor.
Está correto o que se afirma em
O iptables é uma ferramenta para administrar regras de firewall e assim filtrar pacotes de redes.
Assinale a opção que contém o comando mais adequado para adicionar uma regra ao firewall em um sistema operacional Linux, de modo a bloquear a entrada de tráfego proveniente do IP 216.239.38.120.
As tecnologias SOAP e REST são largamente utilizadas para troca de informações estruturadas em sistemas distribuídos.
Sobre essas tecnologias, analise as afirmativas a seguir.
I. REST pressupõe que cada solicitação do cliente ao servidor deve conter todas as informações necessárias para processar o pedido e não pode tirar proveito de qualquer contexto armazenado no servidor.
II. As mensagens SOAP são documentos XML construídos especificamente para trafegar através do protocolo de transporte HTTP/HTTPS.
III. REST é mais eficiente que o SOAP porque utiliza exclusivamente mensagens menores no formato JSON.
Está correto o que se afirma em
O arquivo httpd.conf é o arquivo de configuração principal do servidor Web Apache. Ele contém diretivas que controlam o funcionamento do servidor.
Assinale a opção que indica a diretiva que pode ser usada para especificar endereço e portas alternativas para o servidor web receber requisições externas.
Considere a declaração do tipo de documento (DTD) a seguir.
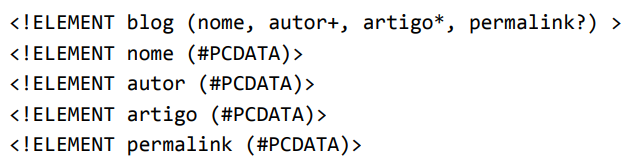
Em um documento XML, que obedece a esse conjunto de regras,
Analise o código a seguir.
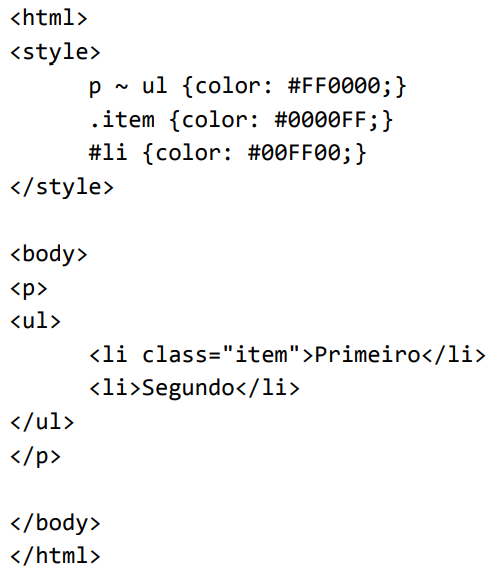
O código determina que as cores da fonte para apresentar as palavras Primeiro e Segundo são, respectivamente,
Sobre padrões de mercado para o fornecimento de serviços de tecnologia da informação, analise as afirmativas as seguir.
I. O modelo do COBIT 5 pressupõe que governança e gestão são disciplinas que compreendem diferentes tipos de atividades, exigem modelos organizacionais diferenciadas e servem a propósitos diferentes.
II. O ITIL v3 sugere o outsourcing como estratégia a ser aplicada quando uma organização não possuir todas as habilidades necessárias para desenvolver e prover um serviço de TI.
III. O PMBOK descreve normas, métodos, processos e práticas para o gerenciamento de projetos com ciclo de vida previsível, sendo, desaconselhável para projetos com ciclo de vida adaptativo.
Está correto o que se afirma em