Questões de Concurso
Para analista de políticas públicas e gestão governamental
Foram encontradas 417 questões
Resolva questões gratuitamente!
Junte-se a mais de 4 milhões de concurseiros!

(Source:http://www.revasolutions.com/internet-of-things-newchallenges-and-practices-for-information-governance/. Retrieved on January 26th, 2018)
Governance Challenges for the Internet of Things
Virgilio A.F. Almeida -Federal University of Minas Gerais, Brazil
Danilo Doneda - Rio de Janeiro State University
Marília Monteiro - Public Law Institute of Brasília
Published by the IEEE Computer Society
© 2015
The future will be rich with sensors capable of collecting vast amounts of information. The Internet will be almost fused with the physical world as the Internet of Things (IoT) becomes a reality. Although it’s just beginning, experts estimate that by the end of 2015 there will be around 25 billion “things” connected to the global Internet. By 2025, the estimated number of connected devices should reach 100 billion. These estimates include smartphones, vehicles, appliances, and industrial equipment. Privacy, security, and safety fears grow as the IoT creates conditions for increasing surveillance by governments and corporations. So the question is: Will the IoT be good for the many, or the mighty few?
While technological aspects of the IoT have been extensively published in the technical literature, few studies have addressed the IoT’s social and political impacts. Two studies have shed light on challenges for the future with the IoT. In 2013, the European Commission (EC) published a study focusing on relevant aspects for possible IoT governance regimes. The EC report identified many challenges for IoT governance — namely privacy, security, ethics, and competition. In 2015, the US Federal Trade Commission (FTC) published the FTC Staff Report The Internet of Things: Privacy and Security in a Connected World. Although the report emphasizes the various benefits that the IoT will bring to consumers and citizens, it acknowledges that there are many risks associated with deploying IoT-based applications, especially in the realm of privacy and security.
[…]
The nature of privacy and security problems frequently
associated with the IoT indicates that further research, analysis,
and discussion are needed to identify possible solutions. First, the
introduction of security and privacy elements in the very design
of sensors, implementing Privacy by Design, must be taken into
account for outcomes such as the homologation process of
sensors by competent authorities. Even if the privacy governance
of IoT can oversee the control centers for collected data, we must
develop concrete means to set limits on the amount or nature of
the personal data collected.
Other critical issues regard notification and consent. If, from one side, it’s true that several sensors are already collecting as much personal data as possible, something must be done to increase citizens’ awareness of these data collection processes. Citizens must have means to take measures to protect their rights whenever necessary. If future scenarios indicate the inadequacy of a mere notice-and-consent approach, alternatives must be presented so that the individual’s autonomy isn’t eroded.
As with other technologies that aim to change human life, the IoT must be in all respects designed with people as its central focus. Privacy and ethics aren’t natural aspects to be considered in technology’s agenda. However, these features are essential to build the necessary trust in an IoT ecosystem, making it compatible with human rights and ensuring that it’s drafted at the measure, and not at the expense, of people.
(Source: https://cyber.harvard.edu/~valmeida/pdf/IoT-governance.pdf
Retrieved on January 23rd, 2018)

(Source:http://www.revasolutions.com/internet-of-things-newchallenges-and-practices-for-information-governance/. Retrieved on January 26th, 2018)
Governance Challenges for the Internet of Things
Virgilio A.F. Almeida -Federal University of Minas Gerais, Brazil
Danilo Doneda - Rio de Janeiro State University
Marília Monteiro - Public Law Institute of Brasília
Published by the IEEE Computer Society
© 2015
The future will be rich with sensors capable of collecting vast amounts of information. The Internet will be almost fused with the physical world as the Internet of Things (IoT) becomes a reality. Although it’s just beginning, experts estimate that by the end of 2015 there will be around 25 billion “things” connected to the global Internet. By 2025, the estimated number of connected devices should reach 100 billion. These estimates include smartphones, vehicles, appliances, and industrial equipment. Privacy, security, and safety fears grow as the IoT creates conditions for increasing surveillance by governments and corporations. So the question is: Will the IoT be good for the many, or the mighty few?
While technological aspects of the IoT have been extensively published in the technical literature, few studies have addressed the IoT’s social and political impacts. Two studies have shed light on challenges for the future with the IoT. In 2013, the European Commission (EC) published a study focusing on relevant aspects for possible IoT governance regimes. The EC report identified many challenges for IoT governance — namely privacy, security, ethics, and competition. In 2015, the US Federal Trade Commission (FTC) published the FTC Staff Report The Internet of Things: Privacy and Security in a Connected World. Although the report emphasizes the various benefits that the IoT will bring to consumers and citizens, it acknowledges that there are many risks associated with deploying IoT-based applications, especially in the realm of privacy and security.
[…]
The nature of privacy and security problems frequently
associated with the IoT indicates that further research, analysis,
and discussion are needed to identify possible solutions. First, the
introduction of security and privacy elements in the very design
of sensors, implementing Privacy by Design, must be taken into
account for outcomes such as the homologation process of
sensors by competent authorities. Even if the privacy governance
of IoT can oversee the control centers for collected data, we must
develop concrete means to set limits on the amount or nature of
the personal data collected.
Other critical issues regard notification and consent. If, from one side, it’s true that several sensors are already collecting as much personal data as possible, something must be done to increase citizens’ awareness of these data collection processes. Citizens must have means to take measures to protect their rights whenever necessary. If future scenarios indicate the inadequacy of a mere notice-and-consent approach, alternatives must be presented so that the individual’s autonomy isn’t eroded.
As with other technologies that aim to change human life, the IoT must be in all respects designed with people as its central focus. Privacy and ethics aren’t natural aspects to be considered in technology’s agenda. However, these features are essential to build the necessary trust in an IoT ecosystem, making it compatible with human rights and ensuring that it’s drafted at the measure, and not at the expense, of people.
(Source: https://cyber.harvard.edu/~valmeida/pdf/IoT-governance.pdf
Retrieved on January 23rd, 2018)

(Source:http://www.revasolutions.com/internet-of-things-newchallenges-and-practices-for-information-governance/. Retrieved on January 26th, 2018)
Governance Challenges for the Internet of Things
Virgilio A.F. Almeida -Federal University of Minas Gerais, Brazil
Danilo Doneda - Rio de Janeiro State University
Marília Monteiro - Public Law Institute of Brasília
Published by the IEEE Computer Society
© 2015
The future will be rich with sensors capable of collecting vast amounts of information. The Internet will be almost fused with the physical world as the Internet of Things (IoT) becomes a reality. Although it’s just beginning, experts estimate that by the end of 2015 there will be around 25 billion “things” connected to the global Internet. By 2025, the estimated number of connected devices should reach 100 billion. These estimates include smartphones, vehicles, appliances, and industrial equipment. Privacy, security, and safety fears grow as the IoT creates conditions for increasing surveillance by governments and corporations. So the question is: Will the IoT be good for the many, or the mighty few?
While technological aspects of the IoT have been extensively published in the technical literature, few studies have addressed the IoT’s social and political impacts. Two studies have shed light on challenges for the future with the IoT. In 2013, the European Commission (EC) published a study focusing on relevant aspects for possible IoT governance regimes. The EC report identified many challenges for IoT governance — namely privacy, security, ethics, and competition. In 2015, the US Federal Trade Commission (FTC) published the FTC Staff Report The Internet of Things: Privacy and Security in a Connected World. Although the report emphasizes the various benefits that the IoT will bring to consumers and citizens, it acknowledges that there are many risks associated with deploying IoT-based applications, especially in the realm of privacy and security.
[…]
The nature of privacy and security problems frequently
associated with the IoT indicates that further research, analysis,
and discussion are needed to identify possible solutions. First, the
introduction of security and privacy elements in the very design
of sensors, implementing Privacy by Design, must be taken into
account for outcomes such as the homologation process of
sensors by competent authorities. Even if the privacy governance
of IoT can oversee the control centers for collected data, we must
develop concrete means to set limits on the amount or nature of
the personal data collected.
Other critical issues regard notification and consent. If, from one side, it’s true that several sensors are already collecting as much personal data as possible, something must be done to increase citizens’ awareness of these data collection processes. Citizens must have means to take measures to protect their rights whenever necessary. If future scenarios indicate the inadequacy of a mere notice-and-consent approach, alternatives must be presented so that the individual’s autonomy isn’t eroded.
As with other technologies that aim to change human life, the IoT must be in all respects designed with people as its central focus. Privacy and ethics aren’t natural aspects to be considered in technology’s agenda. However, these features are essential to build the necessary trust in an IoT ecosystem, making it compatible with human rights and ensuring that it’s drafted at the measure, and not at the expense, of people.
(Source: https://cyber.harvard.edu/~valmeida/pdf/IoT-governance.pdf
Retrieved on January 23rd, 2018)
Mark the statements below as true (T) or false (F) according to Text II:
( ) There are already many studies on the social and political effects of the IoT.
( ) Research studies on security and privacy still need to be carried out.
( ) The report from the US Federal Trade Commission supported the unrestricted use of the IoT.

(Source: http://www.information-age.com/approach-cloud-computingcyber-security-2017-123466624/ Retrieved on January 26th, 2018)
How to approach cloud computing and cyber security in 2017
The adoption of cloud computing has been on the up since as far back as 2008, when a survey conducted by the Pew Research Institute found that cloud services were used by nearly 69% of Americans. Since then, the industry has experienced hypergrowth and exceeded the already vast predictions of how big it would become.
IDC predicts that the cloud computing market in 2017 will be worth $107 billion and, according to Gartner, by 2020 a corporate ‘no-cloud’ policy will be as unusual as a ‘no-internet’ policy would be today. Indeed, it would be difficult to imagine an organisation in 2017 that did not use webmail, file sharing and storage, and data backup.
As the use of cloud computing spreads so does awareness of the associated risks. At the time of writing, there have been 456 data breaches worldwide this year according to the Identity Theft Resource Center (ITRC). The ITRC also noted a 40% increase in data breaches in 2016 compared to the previous year. Yet, despite the well-documented cases of data breaches, organisations continue to invest in and adopt cloud computing services because the benefits usually outweigh the risks.
To understand why the growth of cloud computing has continued in the face of high-profile data breaches, look first to what it can offer an organisation.
Cheaper, bigger, better
Cloud computing is a virtual environment that can adapt to meet user needs. It is not constrained by physical limits, and is easily scalable – making it an obvious choice for start-ups. Cloud computing makes state-of-the-art capability available to anyone with an internet connection and a browser, reducing hardware and IT personnel costs.
Cloud services and software applications are managed and upgraded off-site by the provider, meaning organisations can access technology they would not have been able to afford to install and manage on their own. The popularity of the cloud essentially comes down to its provision of advanced, nextgeneration IT resources in an environment that is cheaper and more scalable than local networks.
The risks involved with cloud computing are mostly securitybased. Clouds are often made up of multiple entities, which means that no configuration can be more secure than its weakest link. The link between separate entities means that attacks to multiple sites can occur simultaneously. When cloud providers do not employ adequate cyber security measures, those clouds become a target for cybercriminals.
Yet, it’s not all bad news. A user survey conducted by one cloud service provider found that concerns about security fell to 25% compared to 29% last year. And as more becomes known about security risks so too does our knowledge around what organisations can do to protect themselves.
(Source: http://www.information-age.com/approach-cloud-computingcyber-security-2017-123466624/. Retrieved on January 25th, 2018)

(Source: http://www.information-age.com/approach-cloud-computingcyber-security-2017-123466624/ Retrieved on January 26th, 2018)
How to approach cloud computing and cyber security in 2017
The adoption of cloud computing has been on the up since as far back as 2008, when a survey conducted by the Pew Research Institute found that cloud services were used by nearly 69% of Americans. Since then, the industry has experienced hypergrowth and exceeded the already vast predictions of how big it would become.
IDC predicts that the cloud computing market in 2017 will be worth $107 billion and, according to Gartner, by 2020 a corporate ‘no-cloud’ policy will be as unusual as a ‘no-internet’ policy would be today. Indeed, it would be difficult to imagine an organisation in 2017 that did not use webmail, file sharing and storage, and data backup.
As the use of cloud computing spreads so does awareness of the associated risks. At the time of writing, there have been 456 data breaches worldwide this year according to the Identity Theft Resource Center (ITRC). The ITRC also noted a 40% increase in data breaches in 2016 compared to the previous year. Yet, despite the well-documented cases of data breaches, organisations continue to invest in and adopt cloud computing services because the benefits usually outweigh the risks.
To understand why the growth of cloud computing has continued in the face of high-profile data breaches, look first to what it can offer an organisation.
Cheaper, bigger, better
Cloud computing is a virtual environment that can adapt to meet user needs. It is not constrained by physical limits, and is easily scalable – making it an obvious choice for start-ups. Cloud computing makes state-of-the-art capability available to anyone with an internet connection and a browser, reducing hardware and IT personnel costs.
Cloud services and software applications are managed and upgraded off-site by the provider, meaning organisations can access technology they would not have been able to afford to install and manage on their own. The popularity of the cloud essentially comes down to its provision of advanced, nextgeneration IT resources in an environment that is cheaper and more scalable than local networks.
The risks involved with cloud computing are mostly securitybased. Clouds are often made up of multiple entities, which means that no configuration can be more secure than its weakest link. The link between separate entities means that attacks to multiple sites can occur simultaneously. When cloud providers do not employ adequate cyber security measures, those clouds become a target for cybercriminals.
Yet, it’s not all bad news. A user survey conducted by one cloud service provider found that concerns about security fell to 25% compared to 29% last year. And as more becomes known about security risks so too does our knowledge around what organisations can do to protect themselves.
(Source: http://www.information-age.com/approach-cloud-computingcyber-security-2017-123466624/. Retrieved on January 25th, 2018)

(Source: http://www.information-age.com/approach-cloud-computingcyber-security-2017-123466624/ Retrieved on January 26th, 2018)
How to approach cloud computing and cyber security in 2017
The adoption of cloud computing has been on the up since as far back as 2008, when a survey conducted by the Pew Research Institute found that cloud services were used by nearly 69% of Americans. Since then, the industry has experienced hypergrowth and exceeded the already vast predictions of how big it would become.
IDC predicts that the cloud computing market in 2017 will be worth $107 billion and, according to Gartner, by 2020 a corporate ‘no-cloud’ policy will be as unusual as a ‘no-internet’ policy would be today. Indeed, it would be difficult to imagine an organisation in 2017 that did not use webmail, file sharing and storage, and data backup.
As the use of cloud computing spreads so does awareness of the associated risks. At the time of writing, there have been 456 data breaches worldwide this year according to the Identity Theft Resource Center (ITRC). The ITRC also noted a 40% increase in data breaches in 2016 compared to the previous year. Yet, despite the well-documented cases of data breaches, organisations continue to invest in and adopt cloud computing services because the benefits usually outweigh the risks.
To understand why the growth of cloud computing has continued in the face of high-profile data breaches, look first to what it can offer an organisation.
Cheaper, bigger, better
Cloud computing is a virtual environment that can adapt to meet user needs. It is not constrained by physical limits, and is easily scalable – making it an obvious choice for start-ups. Cloud computing makes state-of-the-art capability available to anyone with an internet connection and a browser, reducing hardware and IT personnel costs.
Cloud services and software applications are managed and upgraded off-site by the provider, meaning organisations can access technology they would not have been able to afford to install and manage on their own. The popularity of the cloud essentially comes down to its provision of advanced, nextgeneration IT resources in an environment that is cheaper and more scalable than local networks.
The risks involved with cloud computing are mostly securitybased. Clouds are often made up of multiple entities, which means that no configuration can be more secure than its weakest link. The link between separate entities means that attacks to multiple sites can occur simultaneously. When cloud providers do not employ adequate cyber security measures, those clouds become a target for cybercriminals.
Yet, it’s not all bad news. A user survey conducted by one cloud service provider found that concerns about security fell to 25% compared to 29% last year. And as more becomes known about security risks so too does our knowledge around what organisations can do to protect themselves.
(Source: http://www.information-age.com/approach-cloud-computingcyber-security-2017-123466624/. Retrieved on January 25th, 2018)

(Source: http://www.information-age.com/approach-cloud-computingcyber-security-2017-123466624/ Retrieved on January 26th, 2018)
How to approach cloud computing and cyber security in 2017
The adoption of cloud computing has been on the up since as far back as 2008, when a survey conducted by the Pew Research Institute found that cloud services were used by nearly 69% of Americans. Since then, the industry has experienced hypergrowth and exceeded the already vast predictions of how big it would become.
IDC predicts that the cloud computing market in 2017 will be worth $107 billion and, according to Gartner, by 2020 a corporate ‘no-cloud’ policy will be as unusual as a ‘no-internet’ policy would be today. Indeed, it would be difficult to imagine an organisation in 2017 that did not use webmail, file sharing and storage, and data backup.
As the use of cloud computing spreads so does awareness of the associated risks. At the time of writing, there have been 456 data breaches worldwide this year according to the Identity Theft Resource Center (ITRC). The ITRC also noted a 40% increase in data breaches in 2016 compared to the previous year. Yet, despite the well-documented cases of data breaches, organisations continue to invest in and adopt cloud computing services because the benefits usually outweigh the risks.
To understand why the growth of cloud computing has continued in the face of high-profile data breaches, look first to what it can offer an organisation.
Cheaper, bigger, better
Cloud computing is a virtual environment that can adapt to meet user needs. It is not constrained by physical limits, and is easily scalable – making it an obvious choice for start-ups. Cloud computing makes state-of-the-art capability available to anyone with an internet connection and a browser, reducing hardware and IT personnel costs.
Cloud services and software applications are managed and upgraded off-site by the provider, meaning organisations can access technology they would not have been able to afford to install and manage on their own. The popularity of the cloud essentially comes down to its provision of advanced, nextgeneration IT resources in an environment that is cheaper and more scalable than local networks.
The risks involved with cloud computing are mostly securitybased. Clouds are often made up of multiple entities, which means that no configuration can be more secure than its weakest link. The link between separate entities means that attacks to multiple sites can occur simultaneously. When cloud providers do not employ adequate cyber security measures, those clouds become a target for cybercriminals.
Yet, it’s not all bad news. A user survey conducted by one cloud service provider found that concerns about security fell to 25% compared to 29% last year. And as more becomes known about security risks so too does our knowledge around what organisations can do to protect themselves.
(Source: http://www.information-age.com/approach-cloud-computingcyber-security-2017-123466624/. Retrieved on January 25th, 2018)
Text I deals with cloud computing and cyber security. In this respect, analyse the following statements:
I. The risks of breaches in cloud computing are minimal.
II. Cloud computing has developed beyond projections.
III. Results of a survey indicate users are becoming more confident about security.
Choose the correct answer:
A Matriz BCG foi utilizada por uma empresa do ramo de alimentos e bebidas para análise de seu portfólio de produtos. Sobre as análises permitidas pela BCG, analise as afirmativas a seguir.
I. Uma marca de biscoito já consolidada no mercado, que gera uma alta receita sem necessidade de alto investimento em marketing, é um exemplo de vaca leiteira.II. Um refrigerante com baixo desempenho em um mercado em declínio é um exemplo de ponto de interrogação.
III. Um doce alocado no grupo das estrelas gera pouco custo para a manutenção da sua fatia de mercado.
Assinale a opção que indica as afirmativas corretas.
No edital de concurso de uma sociedade de economia mista existe a exigência de que o candidato possua 6 meses de experiência mínima na área do cargo especificado.
Conforme a perspectiva da gestão por competências, essa exigência está relacionada à competência
Após obter com especialistas as estimativas temporais “otimista”, “pessimista” e “mais provável” para um projeto, o gerente de projetos, baseado nas interfaces e interações das várias etapas, chega ao valor ponderado.
Assinale a opção que indica a ferramenta por ele utilizada.
O Prefeito, entusiasmado com a criação de uma Controladoria Geral do Município durante sua gestão, decide fazer a divulgação da novidade por meio de outdoors espalhados pelo centro da cidade.
Em relação à conduta do Prefeito, considerando a perspectiva dos elementos da comunicação, assinale a afirmativa correta.
Uma nova lei é editada prevendo que todos os novos taxistas, a partir da edição da lei, deverão ter curso superior.
Conforme a concepção do modelo das 5 forças proposto por Michael Porter, essa medida pode ser entendida como
Analise o gráfico do ciclo de vida de um projeto, proposto pelo guia PMBOK, a seguir.
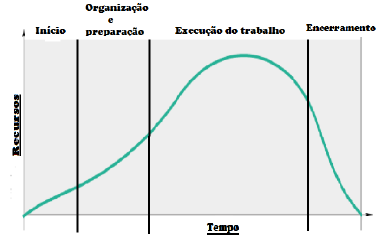
Sobre as fases do ciclo de vida de um projeto, assinale a afirmativa correta.
Ao analisar os indicadores estratégicos de sua companhia, João Pedro verificou que as faltas dos funcionários eram um problema recorrente.
Em relação ao mapa estratégico, a companhia possui uma situação adversa sob a perspectiva
Leia a frase a seguir.
“As Lojas Piririco têm o prazer de anunciar o apoio ao projeto social ´música para todos´ na comunidade Vila Carente”.
A frase pode ser considerada um exemplo de comunicação
Um empresário do setor de commodities, após participar de um workshop sobre gestão, decide aplicar uma política salarial em sua empresa pela qual todos receberiam um salário base mais uma comissão em função da produtividade, pautando-se na ideia de que os esforços são exclusivamente relacionados aos incentivos financeiros.
Esse entendimento do empresário tem influência da
Eugênia, para adotar um estilo de liderança mais adequado em uma organização não governamental (ONG) de proteção dos direitos humanos, decidiu fazer uma pesquisa sobre o assunto na Biblioteca Municipal.
Após alguns dias, Eugênia se depara com o modelo denominado continuum de liderança e verifica que precisa analisar três conjuntos de forças para encontrar o estilo de liderança mais adequado para seu contexto.
Assinale a opção que os indica.
Visando reduzir o número de assaltos na cidade, a Prefeitura lança um aplicativo para celular que conta com a colaboração da população para notificar onde ocorreram assaltos, criando assim um mapa regional do crime.
Decorrido 1 ano do lançamento do aplicativo, a Prefeitura elabora um diagrama de dispersão para avaliar a utilidade do aplicativo.
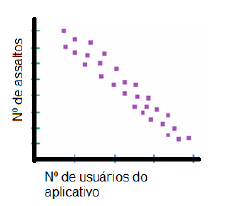
De acordo com o diagrama apresentado, assinale a afirmativa correta.