Questões de Concurso Público AL-MG 2023 para Analista Legislativo - Analista de Sistemas II - Administração de Rede e Suporte Técnico
Foram encontradas 60 questões
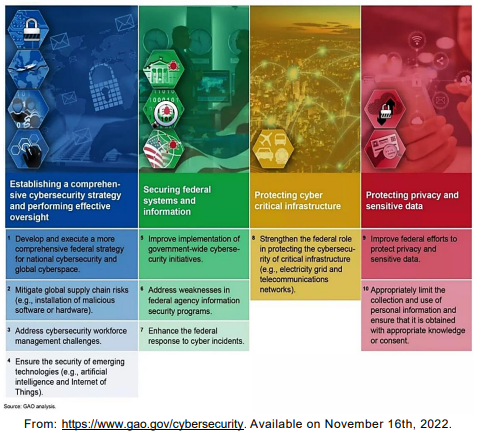
Cybersecurity: An overview of cyber challenges facing the nation, and actions needed
Federal agencies and the nation’s critical infrastructure — such as energy, transportation systems, communications, and financial services — depend on Information Technology (IT) systems to carry out operations and process essential data. However, the risks to these IT systems are increasing—including insider threats from witting or unwitting employees, escalating and emerging threats from around the globe, and the emergence of new and more destructive attacks. Rapid developments in new technologies, such as artificial intelligence, the Internet of Things, and ubiquitous Internet and cellular connectivity, can also introduce security issues. Over 28,000 security incidents were reported by federal civilian agencies to the Department of Homeland Security in FY 2019.
Additionally, since many government IT systems contain vast amounts of personally identifiable information (PII), federal agencies must protect the confidentiality, integrity, and availability of this information—and effectively respond to data breaches and security incidents. Likewise, the trend in the private sector of collecting extensive and detailed information about individuals needs appropriate limits.
To highlight the importance of these issues, Government Accountability Office (GAO) has designated information security as a government-wide high-risk area since 1997. This high-risk area was expanded in 2003 to include the protection of critical cyber infrastructure and, in 2015, to include protecting the privacy of PII.
GAO has made about 3,300 recommendations to federal agencies to address cybersecurity shortcomings—and we reported that more than 750 of these had not been fully implemented as of December 2020. We designated 67 as priority, meaning that we believe they warrant priority attention from heads of key departments and agencies.
Adapted from: https://www.gao.gov/cybersecurity. Available on November 16th, 2022
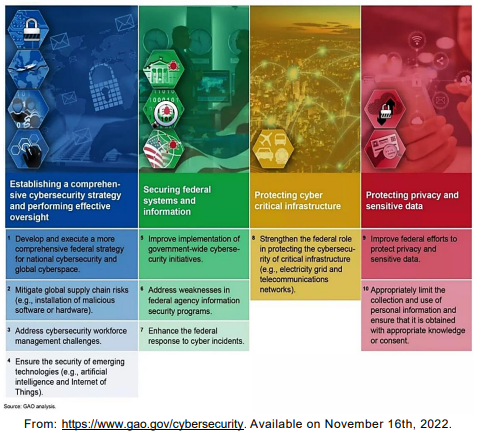
Cybersecurity: An overview of cyber challenges facing the nation, and actions needed
Federal agencies and the nation’s critical infrastructure — such as energy, transportation systems, communications, and financial services — depend on Information Technology (IT) systems to carry out operations and process essential data. However, the risks to these IT systems are increasing—including insider threats from witting or unwitting employees, escalating and emerging threats from around the globe, and the emergence of new and more destructive attacks. Rapid developments in new technologies, such as artificial intelligence, the Internet of Things, and ubiquitous Internet and cellular connectivity, can also introduce security issues. Over 28,000 security incidents were reported by federal civilian agencies to the Department of Homeland Security in FY 2019.
Additionally, since many government IT systems contain vast amounts of personally identifiable information (PII), federal agencies must protect the confidentiality, integrity, and availability of this information—and effectively respond to data breaches and security incidents. Likewise, the trend in the private sector of collecting extensive and detailed information about individuals needs appropriate limits.
To highlight the importance of these issues, Government Accountability Office (GAO) has designated information security as a government-wide high-risk area since 1997. This high-risk area was expanded in 2003 to include the protection of critical cyber infrastructure and, in 2015, to include protecting the privacy of PII.
GAO has made about 3,300 recommendations to federal agencies to address cybersecurity shortcomings—and we reported that more than 750 of these had not been fully implemented as of December 2020. We designated 67 as priority, meaning that we believe they warrant priority attention from heads of key departments and agencies.
Adapted from: https://www.gao.gov/cybersecurity. Available on November 16th, 2022
What is the best alternative to fill the gaps to complete this conditional sentence?
“Until cybersecurity shortcoming ______ addressed, federal and critical infrastructure IT systems _______ increasingly susceptible to cyber threats.”
What is the BEST alternative to fill the gaps to complete this conditional sentence?
Ten critical actions needed to address four major cybersecurity challenges:
The use of the preposition for in “1. Develop and execute a more comprehensive
federal strategy for national cybersecurity…” indicates
Ten critical actions needed to address four major cybersecurity challenges:
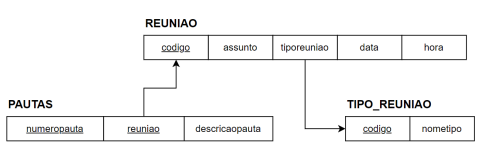
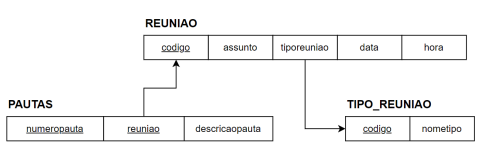
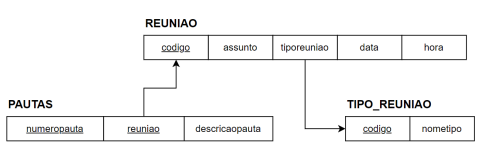
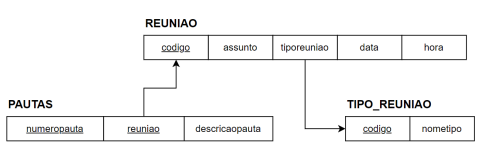
Em relação ao esquema de banco de dados relacional, analise as seguintes afirmativas.
I. A chave primária da relação PAUTAS é “numeropauta”.
II. O atributo “codigo” da relação TIPO_REUNIAO é chave primária e também chave estrangeira.
III. O atributo “reuniao” da relação PAUTAS é uma chave estrangeira.
Está CORRETO apenas o que afirma em:
Analise as afirmativas referentes às estruturas de dados básicas:
I – Uma lista linear é uma sequência de zero ou mais itens x1, x2, ..., xn, em que xi é de um determinado tipo e n representa o tamanho da lista linear.
II – Uma pilha é uma lista linear em que todas as inserções, retiradas e geralmente todos os acessos, são feitos em apenas um extremo da lista.
III – Uma fila é uma lista linear em que todas as inserções são realizadas em um extremo da lista e todos os acessos e retiradas são realizados no mesmo extremo da lista.
Estão CORRETAS as afirmativas:
Considere a figura a seguir representando um vetor e os passos de um método de ordenação interna.
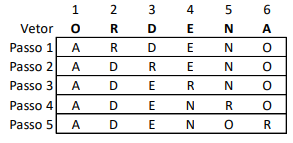
Analise as afirmativas referentes ao método de ordenação interna utilizado para ordenar o vetor:
I – O método apresentado é baseado no princípio da distribuição.
II – O método apresentado requer O(n2) comparações.
III – O método apresentado é um exemplo de ordenação por seleção.
Estão CORRETAS as afirmativas:
Analise as afirmativas referentes à Lei Geral de Proteção de Dados Pessoais (LGPD):
I – Anonimização é o tratamento por meio do qual um dado perde a possibilidade de associação, direta ou indireta, a um indivíduo, senão pelo uso de informação adicional mantida separadamente pelo controlador em ambiente controlado e seguro.
II – Consentimento é a manifestação livre, informada e inequívoca pela qual o titular concorda com o tratamento de seus dados pessoais para uma finalidade determinada.
III – Bloqueio é a suspensão temporária de qualquer operação de tratamento, mediante guarda do dado pessoal ou do banco de dados.
Estão CORRETAS as afirmativas: